Posts in category Beyond Delft
Bitcoin and scalability
For the past few months, questions about the scalability of Bitcoin has been increasing and the developer community has attempted to come up with a solution. But the Bitcoin community is divided over the solutions and as mentioned here, it seems like an election where things are getting heated. As Bitcoin is based on consensus, a change cannot be made if a consensus is not reached.
Currently Bitcoin handles about 7 transactions per second while it has been claimed that the number is lower. Compare this to the 4000 transactions/second that VISA can handle, we see the gap in scalability. In order to scale Bitcoin, increasing the maximum block size (which is currently 1MB) is a necessity. More complex solutions, such as Segregated Witness proposed by Pieter Wuille at Scaling Bitcoin Conference in Hong Kong last December has found support in the community. Segregated Witness removes the signature from the transaction and stores it in a separate data structure, thus reducing the size of the transaction.
Gavin Anderson describes in his blog,
For example, the simplest possible one-input, one-output segregated witness transaction would be about 90 bytes of transaction data plus 80 or so bytes of signature– only those 90 bytes need to squeeze into the one megabyte block, instead of 170 bytes. More complicated multi-signature transactions save even more.
But why is Bitcoin scalability important? The Bitcoin network is congested and small increase in traffic leads to “dramatic changes in network conditions”. Transactions take minutes and sometimes hours to be executed. How many users find it acceptable to wait that long for their transactions to be executed?
Currency to Cryptocurrency
Bitcoin is a cryptocurrency, a digital currency which uses cryptography to create money and secure transactions. The transactions are processed in a decentralized manner such that the users do not need to trust any single party. The transactions are recorded in a blockchain which is a public ledger and can be cryptographically verified by anyone. This is a fascinating concept and one can find many resources to read about it, starting with Satoshi Nakamoto’s paper.
But before understanding bitcoins, there is one question that needs to be asked. What is money? And where does is come from? In the book Atlas Shrugged, Ayn Rand wrote,
Have you ever asked what is the root of money? Money is a tool of exchange, which can’t exist unless there are goods produced and men able to produce them. Money is the material shape of the principle that men who wish to deal with one another must deal by trade and give value for value. Money is not the tool of the moochers, who claim your product by tears, or of the looters, who take it from you by force. Money is made possible only by the men who produce.
It is a common notion that money is a commodity. But is it? Money can take multiple forms. Money can can take the form of commodity, paper or merely a value. The video below explains the transition from gold standard to fiat currency to bitcoin.
Below is a video [from 1:35 till 2:50] where a person with no prior experience with money finds it hard to grasp why the image in only a particular form (bank note) is of value and not otherwise. [I think the scene conveys the message even if one does not understand the dialogues]
Finally a video on what gives money its value.
Zimmerman Telegram
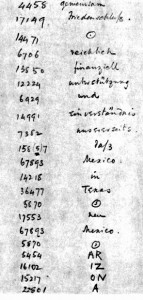
On the interception of the Zimmerman telegram, the German diplomatic code 0075 was noticed by the British. Kahn mentions in (Kahn, 1967), Room 40 knew from its analyses that 0075 was one of a series of two-part codes that the German Foreign Office designated by two zeros and two digits, the two digits always showing an arithmetical difference of 2. Among the others, some of which Room 40 had solved, were 0097, 0086, which was used for German missions in South America, 0064, used between Berlin and Madrid and perhaps elsewhere, 0053, and 0042.” Initially only part of the long message was deciphered. But Zimmerman’s signature could be read. Code 0075 was a two-part code of 10,000 words and phrases numbered 0 to 9999 in mixed order. This was a gigantic monoalphabetic substitution cipher where instead of 26 alphabets, thousands of codes with low frequency were involved and whose characteristics were less defined than English alphabets. When a Code is intercepted, the initial identifications are first marked by pencil and placed in “pencil groups”. When confirmed by further traffic, they are placed in “ink groups”. But Room 40 did not have enough Code 0075 messages to decipher the Zimmerman telegram in total. Zimmerman telegram was partially deciphered but enough to obtain the core of the message. Though US entry into the war would have helped the Allies, there were enough arguments against informing the US. First, Room 40 was one of Britain’s darkest secrets. If a partially deciphered message is sent to the US, it would expose “Room 40”. Second, this would expose Britain’s habit of supervising telegrams of neutrals Third, this would lead to Germany using new codes instead of 26 alphabets, thousands of codes with low frequency were involved and whose characteristics were less defined than English alphabets.
The chief of Room 40, W.R. Hall, then devised a plan to obtain the telegram from Mexico. He thought that the German mission in Mexico may not have Code 0075 and might use an older code. He obtained a copy of the Zimmerman telegram as received in Mexico and realised that Code 13040, which was an older code, was used to encipher. This code was easier to decipher as Room 40 had intercepted many transmissions using the same code. A portion of the decrypted code is shown below. It can be observed that the word Arizona is not in the German codebook and has been split into phonetic syllables.
Hall showed the message to the secretary of the US embassy after few days. The secretary of the US embassy in Britain then sent the message to the US President. He himself did not know of the existence of Room 40 but wanted to keep his involvement secret. The authenticity of the telegram was initially doubted by the US government. But all doubts were eliminated by Zimmerman himself when he admitted to having sent the telegram (Boghardt, 2003). The telegram was published in newspapers and the citizens of US, who were initially against the war, pushed the government to participate in the war. The US involvement reinforced the Allied troops. “Room 40” was merged with British Intelligence unit MI1b to form Government Code and Cypher School which was later renamed as Government Communications Headquarters (GCQC).
References:
Kahn, David (1967), The Code Breakers: The Story of Secret Writing, Weidenfeld and Nicolson.
Boghardt, Thomas (2003), The Zimmermann Telegram: Diplomacy, Intelligence and The American Entry into World War I (PDF). Working Paper Series. Washington DC: The BMW Center for German and European Studies Edmund A. Walsh School of Foreign Service, Georgetown University. 6-04.
Room 40
In August 1914, British cable ship Telconia entered the North Sea and the men on-board cut the transatlantic cables and hence cut-off Germany from communicating through wired lines to the rest of the Western Europe and USA (Kahn, 1967). This forced Germany to use radio for all communication or use cables controlled by the Allies and hence allowed the Allies to intercept. In contrast, the British and French used wireless to communicate with ships at sea and not otherwise.
But Britain had no formal codebreaking organization even though intercepts were piling up. The Director of Naval Education, Alfred Ewing, put together a team of mostly volunteers from naval colleges to work on the intercepts. But they made no real progress. It was in September 1914 that the German cruiser Megdeburg was wrecked in Baltic and the Russians were able to obtain two cipher and signalling books from a drowning German officer. The Russians gave one of the books to the British. But Ewing’s team could not find any correlation between the four letter words in the books and the intercepts. Later it was found that the code had been superenciphered by monoalphabetic substitution. With the codebook in possession, deciphering became easy. Some codewords appeared more frequently, allowing for frequency analysis. Also the consonants appeared alternately with the vowels in the German codewords. The British acquired two more codebooks, one from a German-Australian steamer, Hobart, and another from the sinking German destroyer SMS S119 in the battle of Texel Island. With increasing number of intercepts and more men being recruited to decipher them, Ewing’s team moved to a large room Room 40, which lead to the organization informally being called Room 40.
Most intercepted messages reported the whereabouts of Allied ships. Though interesting, this information was not vital to the British. They recognized that the Germans also used short wave which the British could not intercept with the available infrastructure. So a station was set up to monitor shortwave signals and information about the movements of the High seas fleet was obtained. Even though it was no secret that the British had access to the codebook, the German’s continued to use the same until mid-1916. The book was massive and it could not be easily changed. But they did increase the frequency of changing the keys for monoalphabetic substitution. At the beginning of the war, the key was changed once in 3 months. In 1916, it was changed every midnight. But Room 40 had developed expertise and only needed few hours to find the new key every day.
Room 40 played an important role throughout the war. Winston Churchill wrote, “Without the cryptographers’ department there would have been no Battle of Jutland”. But the most important contribution of Room 40 was to decipher the Zimmerman telegram in 1917 which lead to America’s entry in the war. In this telegram, the German Foreign Minister Arthur Zimmerman offered Mexico the territories of Texas and Arizona if they join the war as a German ally. The message was sent from the US embassy in Berlin through Copenhagen and London to the German embassy in Washington. It was to be retransmitted to Mexico from there. The message read as follows:
We intend to begin on the first of February unrestricted submarine warfare. We shall endeavor in spite of this to keep the United States of America neutral. In the event of this not succeeding, we make Mexico a proposal of alliance on the following basis:Make war together, make peace together, generous financial support and an understanding on our part that Mexico is to reconquer the lost territory in Texas, New Mexico, and Arizona. The settlement in detail is left to you. You will inform the President [of Mexico] of the above most secretly as soon as the outbreak of war with the United States of America is certain and add the suggestion that he should, on his own initiative, invite Japan to immediate adherence and at the same time mediate between Japan and ourselves. Please call the President’s attention to the fact that the ruthless employment of our submarines now offers the prospect of compelling England in a few months to make peace.
Zimmerman
Reference:
Kahn, David (1967), The Code Breakers: The Story of Secret Writing, Weidenfeld and Nicolson
Implication of ‘Human Chipping’ on personal identity – Part 2: Are we artificial by nature?
Most human beings will consider implantation of RFID chips in the body as unnatural. But what is natural? One could say that what we are when we are born and the genetic information that we pass on to our children is natural. We are born naked, but we wear clothes to keep ourselves warm. Clothes are not natural to us. We are deprived of properties such as think skin or fur which many other animals have (Gehlen, 2003). We fulfill our requirements using technology.
It is natural that people contract diseases such as cancer and AIDS. Earthquakes and hurricanes are natural disasters. But these are not necessarily good for human beings. If it is possible to improve the situation through technological intervention, then why not? Like all changes in the society be it technological or not, the benefits are countered by the negatives. If the benefits outweigh the negatives then transhumanists would claim that there is no necessity for being skeptical about the technology (Bostrom, 2007).
Aristotle said that nature is grown while technology is made. Habermas claims that these categories de-differentiate when we interfere with nature (Habermas, 2003). He says humans should act morally as self-creating and autonomous beings. He claims that intervention leads to one category of ‘programmers’ and another of ‘programmed’. The ‘programmer treats the other person as object and has an attitude of domination while the ‘programmed’ will feel less free and lose autonomy as the attitude and behavior will be encoded. If Habermas’ categorization is applied to ‘Human Chipping’, the person or the organization who are implanting RFID chips on other human beings are the ‘programmers’ while the person with the implant is the ‘programmed’.
Let us consider the situation where newly born children are implanted with RFID chips. Initially these chips are used for identifying the infant in the hospital. This chip would be useful to monitor the health of the child throughout its life. Here there is no possibility of informed consent though. So the ‘programmed’ has no autonomy on choosing if it wants to be programmed or not. Humans are ‘by nature’ artificial and have no ‘natural origin’ and thus humans are a prosthetic being. Human evolution is the result of technical exteriorization of life. Humans are not autonomous but are ‘programmed’ by technology (Stiegler, 1998).
References:
Bostrom, N. (2007). In Defense of Posthuman Dignity. Bioethics, 206-214.
Gehlen, A. (2003). A Philosophical Anthropological perspective on technology. In R. C. Dusek, Philosophy of Technology: The Technological Condition: An Anthology (pp. 213-220). Blackwell Publishers.
Habermas, J. (2003). The Future of Human Nature. Polity Press.
Stiegler, B. (1998). Technics and Time: The fault of Epimetheus. Stanford University Press.
Implication of ‘Human Chipping’ on personal identity – Part 1: Are we Cyborgs?
The first RFID implant on a human being was performed in August of 1998 on the upper left arm of Professor Kevin Warwick in Reading, England (Gasson, ICT Implants, 2008). The implant was cylindrical in structure having a length of 22mm and diameter of 4mm. The doctor required to make a small hole, place the RFID chip and close the incision with couple of stitches. The implant allowed Professor Warwick to control lights, open doors and even receive welcome messages when he arrived. His location in the building could be tracked and monitored. This was only experimental and hence other possible applications of the technology were not considered by the scientists at that time.
One of the first commercial application of RFID chips was to replace ‘medic alert’ bracelets by VeriChip Corporation in 2004 (Gasson, ICT Implants, 2008). It was approved by the FDA in the United States of America for human use. It was used to relay medical details when linked to online medical database. For example, the details of the patient’s diabetes can be stored in the chips and because it is implanted, the patient cannot forget it or lose it. Later on the company also used these chips for infant protection and patient monitoring in hospitals. Subsequently these chips were used by nightclubs in Barcelona and Rotterdam to allow access to their VIP members. For example, at the Baja Beach Club in Rotterdam, these chips were implanted in their VIP members and were used for not only entry into the club but also for ordering drinks. For instance, if a member bought a drink, the chip could be read by an RFID reader and the amount can be deducted from the bank directly without the member getting hands on his/her wallet.
In these applications of ‘Human Chipping’, it can be seen that these RFID chips become a permanent part of the person. A person who has an RFID Chip in his arm for some time would become used to its functionality and would not think of it as an electronic component but instead as a part of his body (Gasson, Human implants from invasive to pervasive at TEDxGoodenoughCollege, 2012). How is the RFID implant any different from a person’s leg, hand or any other part of the body? If a person loses their legs in an accident, he will not be able to walk. If prosthetic legs are used he would be able to walk again. These prosthetic legs are made to function as legs such that the person is not able to differentiate it from his legs. They become a part of the person and not as an external component that he has worn. Similarly for the person whose diabetes is being monitored by the RFID implant, the chip becomes a part of the body. If the chip is removed, then the person’s existence would become difficult. His body will not function properly. If we are considering the chip as part of the body, aren’t we cyborgs?
One experiment done by researchers from Vrije University in Amsterdam amplifies the argument that we have become cyborgs. Their experiment involved placing a malicious computer code on a RFID tag, so that if the tag is read by the building system it would get infected by the virus (Rieback, Crispo, & Tanenbaum, 2006). Depending on the virus, it could disrupt the functioning of the building system or spread the virus to the tags used by others. Though this experiment sheds light on the security issues of the technology, we can look at its implications on personal identity. The spread of the computer virus using the implant is analogous to the spread of a communicable disease such as tuberculosis. The virus originates from the RFID tag implanted in a person and passes on to others. It is not possible to separate the RFID tag from the person and say that the virus originated from the tag but not from the person. Think of a situation in which this computer virus corrupts the functioning of every RFID chip that it infects. It might be fatal to a person whose insulin intake is dependent on the RFID chip. This could be a criminal offence but only if the chip is considered as part of the offender, which would make the offender a cyborg.
References:
Gasson, M. (2008). ICT Implants. The Future of Identity in the Information Society, 262, pp. 287-295. Retrieved from BBC: http://www.19.bbc.co.uk
Gasson, M. (2012). Human implants from invasive to pervasive at TEDxGoodenoughCollege. Retrieved from TedX: http://tedxtalks.ted.com/video/Human-implants-from-invasive-to
Rieback, M., Crispo, B., & Tanenbaum, A. (2006). Is your cat infected with a computer virus? IEEE International Conference on Pervasive Computing and Communication, (pp. 169-179).
Technological implants- Therapy or Enhancement?
Technological implants in human beings is not a new phenomenon. The pacemaker is used by many people around the world to help their heart function appropriately. For the past few years, cochlear implants have been performed on people whose hair cells in the inner ear become unresponsive. In this case the implant acts as a replacement for the lost functionality of hair cells. In both these examples, technology is used as a therapy in order to assist in normal functioning of the human being. In the case of cochlear implants, it has been observed that the person with the implant takes few weeks or months to get used to it. It is claimed that though the person is able to hear sounds again, the sounds that they hear is different from what they had experienced before going deaf. In the case of a child which is born deaf, the sounds heard due to the cochlear implant will be the only sounds known. Technology here is a mediator in helping humans achieve their goal of being able to hear sounds. There is no original perception mediated by technology but the mediated perception itself is the original (Ihde, 1990). But what if cochlear implants allowed humans to hear ultrasonic sounds. Humans without cochlear implants cannot hear ultrasonic sounds. In this case, would cochlear implants be a form of therapy or enhancement?
One of the first commercial application of RFID implants was in the field of medicine in order to monitor the patient. This would be considered as a therapy by the hospital. But if we consider the umpteen number of people who do not have access to such technology but have the same diseases, it does seem that patients with implant are privileged and that the implant is an enhancement to their functioning as human beings. Some might say that the privileged ones are ‘better than normal’ (Kurzweil, 2005). They can upload their information or data into the database of the hospital through the internet unconsciously. They don’t need to click a button to send the information. In certain regards, they are uploading a part of themselves which could be looked upon as extending their memory (Clark & Chalmers, 1998). They may not consciously know or remember their current blood sugar level but the medical database of their hospital is updated with the information that can be accessed later if needed.
One possible application of RFID chips would be to implant them on finger tips of a person. Let us consider that a policeman is implanted with an RFID chip containing an infrared sensor, which senses heat, on the index finger of his right hand. If he is entering a house which is dark to catch a crime suspect, he can find in which direction the suspect is by just spatially moving his hand. This gives him additional power compared to his colleagues and is certainly an enhancement to his ‘human qualities’. But Professor Mark Gasson from Reading University has a different view. He does not consider the implants as an enhancement (Gasson, Human implants from invasive to pervasive at TEDxGoodenoughCollege, 2012). Though very few people have RFID implants now, he thinks that soon almost everyone will have it. He compares RFID implants to mobile phones. Earlier very few used mobile phones but in a few years almost everyone in developed and developing nations considers it as a necessity and feels out of place if they do not have a mobile phone. It is possible that in the near future, implants may not remain optional but may become compulsory.
References:
Clark, A., & Chalmers, D. J. (1998). The Extended Mind. The Philosopher’s Annual, XXI, 10-23.
Gasson, M. (2012). Human implants from invasive to pervasive at TEDxGoodenoughCollege. Retrieved from TedX: http://tedxtalks.ted.com/video/Human-implants-from-invasive-to
Ihde, D. (1990). Technology and the lifeworld. Indiana University Press.
Kurzweil, R. (2005). The singularity is near: When humans transcend biology. Viking/Penguin Group
What is Privacy?
Over the past couple of years, “privacy” has received widespread media coverage. Some people say that if one does not have anything to hide, then there is no need of privacy. A lot has been written about the amount and kind of data collected by corporations. It is said that there is no need to worry as only metadata is collected and not the data itself. What it really means is that, users have lower level of protection by law as compared to a situation where data is being collected. In an earlier article here I have written how metadata can sometimes provide more information than the data itself. But what is “privacy”?
The first legal article on privacy titled “The Right to Privacy” was published in 1890 by Samuel Warren and Louis Brandeis. In this article they discuss privacy as the “right to be let alone”. They also mention “Numerous mechanical devices threaten to make good the prediction that ‘what is whispered in the closer shall be proclaimed from the house tops.’” In the same year William James addressed the idea of being able to present ourselves to different people by withholding private information.
Another way of looking at privacy is by using the metaphor used by Erving Goffman in his book “The Presentation of self in Everyday Life”. He writes that society is a stage in which we are actors. But as with most stages, there is a backstage, an area which is invisible to the public, where we do things not to be presented to the public. Privacy plays the role of allowing us to prepare for the presentation before going on to the stage.
Stephen B. Wicker mentions that privacy could be thought in terms of observability and controllability in control theory. Controllability denotes acquiring enough information so that the system can be driven to the desired state. An example would be personalized advertisement. If the advertiser has enough information about the person, then the advertisements viewed by the person would be suited to the needs and the advertiser would reap benefits.
In 2009, Helen Nissenbaum wrote a book “Privacy in Context” in which she introduces the idea of contextual integrity. She maintains that we control the personal information we want to hold by having a boundary. In addition she uses the metaphor of a zone of seclusion, in which the control is handled differently depending on the context and the person’s perception of solitude. This includes that the person is able to exercise various thoughts without worrying of censure.
Implicit dualism
It can be commonly observed that human beings, with few exceptions, have a dualistic way of thinking and speaking. According to Aristotelian logic it has to be either true or false. But should it be the case? Dualism could be explicit but it could also be implicit. How would you answer the above question about logic? Yes or No or both?
Dualism implicitly creeps into speech. For example ‘It is a sunny day’, ‘This statement is false’, etc. The listener seems to be left in the position of agreeing or disagreeing. On closer inspection it can be observed that both statements contain the word ‘is’. The first example ‘It is a sunny day’ could be considered dualistic. But what if it is intermittently raining throughout the day though sunshine makes its presence felt for most part of the day. Can it not be both a rainy and sunny day? Can the truth not be restricted to just two boxes?
The second example ‘This statement is false’ appears paradoxical. If it is true that the sentence is false, then it contradicts itself. If it has to be true that it is false that it is true that it is false and so on. How can this contradiction be solved by Aristotelian logic? One possible way would be to restate the sentences in E-prime (a prescriptive version of English language which excludes all forms of ‘to be’).
The use of E-prime can be critical in some situations. If a person is witness to a hit and run accident, he/she could state ‘The car involved in the accident was a black Hummer’ or in E-prime ‘The car involved in the accident appeared to be a black Hummer.’ The former statement gives an impression of surety and absolute which might not be the case. The latter statement is not absolute and informs the listener that the colour and make of the car were as interpreted and remembered.
E-prime appears to be just one way to make thoughts and speech more flexible and less dualistic.
Penrose Stairs Image Source: http://r-boisard.deviantart.com/art/Penrose-stair-243885764
A Wealth of Information
“A Wealth of information creates a poverty of attention”
– Herbert Simon
In some parts of the world, it is assumed that most people who want and can afford, have access to the internet. I see advertisements saying “Rent includes internet. Who lives without internet these days?” I would say that the person who has placed the advertisement is living in a bubble. But does this person need to know about everything in the world? Over the past couple of years hundreds of Exabyte’s of information has been added.
Let us say that you are one of those who has the urge to know a little of everything that is happening in this world. You access news articles daily, probably watch news on television, read variety of books, follow “important” personalities on twitter, regularly check your emails, instant messages, watch new and old movies and search for other information on “popular” search engines. You are flooded with spam mails and advertisements as well. How much of this information do you need? What is the signal-to noise ratio? In addition you may not realise that you are living in a “filter bubble”.
Information pollution has an impact on individuals, businesses and society at large. But how can you reduce the impact of information pollution? Until unless you have read a book or watched a movie you don’t know if it is useful to you or not. Many corporations restrict usage of social media access of their employees during working hours. The question arises, why does anyone want to access social media sites while working? This is one example of continuous partial attention (CPA), in which a person is simultaneously paying attention to multiple information sources. Often it is an automatic process due to habit and not a conscious one.
The concept of attention economy discusses the abundance of information and how its immediate availability limits the human ability to process the information. This has lead to corporations incorporating intangibles such as personalization, ease of access and immediacy to attract consumers as reproduction of information does not cost anything.
In this ocean of information, how much is enough?